This CloudMapper post introduces the sg_ips command which identifies the external CIDR’s that are trusted in your security groups and performs geoip look ups against them. It displays a list of the CIDR ranges with any descriptions they have from the security groups, their physical locations in the world, and the ASN associated with them, which is often the ISP or company that owns the IP range.
This can be useful for spotting trusted access that is no longer needed (ex. when someone decided to give their hotel room trusted access during a conference trip) or a vendor that you didn’t realize was outsourcing their work and access to an unexpected location.
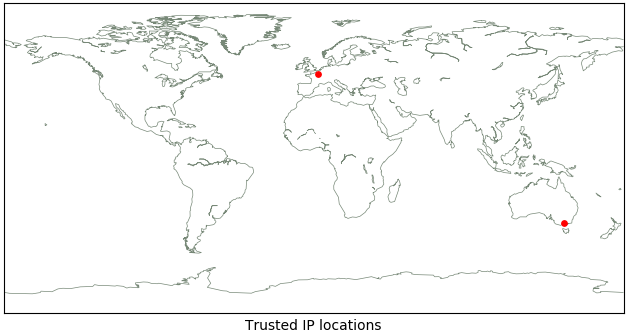
Here is an example of the output and image it generates:
$ python cloudmapper.py sg_ips --account demo
1.1.1.1/32 Research, Victoria, Australia Cloudflare Inc
2.2.2.2/28 France Orange
Image saved to /tmp/cloudmapper/trusted_ips.png
In this example, CloudMapper has identified that our demo account trusts the CIDRs 1.1.1.1/32 and 2.2.2.2/28. It then performed geoip look-ups in order to identify these IPs are in Australia and France, owned by Cloudflare and Orange, and then generated the world map with red dots showing the locations of these CIDRs.
Only the first IP in the range is used for identification. The MaxMind database is used for the geoip lookups and needs to be download locally as explained later.
Like the stats command, you can get info on multiple accounts at once using an argument like --account dev,stage,prod.
Auditing
As sg_ips runs, it will perform a couple of checks on the CIDR ranges it looks like at, including:
- Identifying large CIDR’s (over 2048 IPs in them)
- Unknown CIDRs that don’t exist in the geoip database
- Unneeded CIDRs such as trusting
127.0.0.1or169.254.169.254which doesn’t do anything on AWS.
In addition to the above, you should review the output for things like:
-
CIDRs being given different descriptions (ex. “bob’s home IP company datacenter”) - CIDRs in unexpected locations
- Overlapping or poorly grouped CIDRs such as
2.2.2.2/28and2.2.2.3/32which could indicate that two Security Groups were originally setup for2.2.2.2/32, but then the IP changed to a different one within the company address space and only one Security Group was opened up for that change.
Setup
This command requires a bit of setup outside of the usual pip install -r requirements.txt.
basemap library install
This command calls from mpl_toolkits.basemap import Basemap so we need to install that library, which unfortunately doesn’t exist in pip. Instructions for doing this are at https://matplotlib.org/basemap/users/installing.html
Getting to the important parts, you’ll need to do the following from your cloudmapper directory:
mkdir -p tmp; cd tmp
curl https://codeload.github.com/matplotlib/basemap/tar.gz/v1.1.0 --output basemap-1.1.0.tar.gz
tar -zxvf basemap-1.1.0.tar.gz
cd basemap-1.1.0/
python setup.py install
cd ..
rm -rf basemap-1.1.0*
cd ..
You should now be able to run the following without issues:
$ python
Python 2.7.10 (default, Oct 6 2017, 22:29:07)
[GCC 4.2.1 Compatible Apple LLVM 9.0.0 (clang-900.0.31)] on darwin
Type "help", "copyright", "credits" or "license" for more information.
>>> from mpl_toolkits.basemap import Basemap
>>>
MaxMind database download
MaxMind kindly makes their “GeoLite2” database available under a “Creative Commons Attribution-ShareAlike 4.0 International License”.
You’ll need to have two files (GeoLite2-ASN.mmdb and GeoLite2-City.mmdb) under data/ in your cloudmapper directory. To do this, run:
mkdir -p data; cd data
# Get city data
curl http://geolite.maxmind.com/download/geoip/database/GeoLite2-City.tar.gz
tar -zxvf GeoLite2-City.tar.gz
mv GeoLite2-City_*/GeoLite2-City.mmdb .
# Get ASN data
curl http://geolite.maxmind.com/download/geoip/database/GeoLite2-ASN.tar.gz
tar -zxvf GeoLite2-ASN.tar.gz
mv GeoLite2-ASN*/GeoLite2-ASN.mmdb .
# Clean up
rm -rf GeoLite2-City_*
rm -rf GeoLite2-ASN_*
rm -rf GeoLite2-*.tar.gz
cd ..
You now should be able to run python cloudmapper.py sg_ips --account demo.
Try it out by cloning CloudMapper from https://github.com/duo-labs/cloudmapper